By B.L. Wilson
One of the greatest threats to the United States is its enormous vulnerability in cybersecurity, according to Sen. Mark Warner (D-Va.), because the federal government has never had a cyber doctrine.
“Our failure to articulate a doctrine, to set out cyber norms, and frankly concern about any cyber escalation, has meant in many ways those near-peer adversaries have felt it has been open season on attacking our country, stealing our intellectual property with very little fear of repercussion,” said Mr. Warner, B.A. ’77.
A case in point, the senator noted, was the recent revelation that Chinese hackers broke into a U.S. Navy system and stole highly sensitive information, as well as the millions of cyber hits the Department of Defense takes daily.
“The level of the attack, the level of seriousness has gotten exponentially higher,” Mr. Warner said.
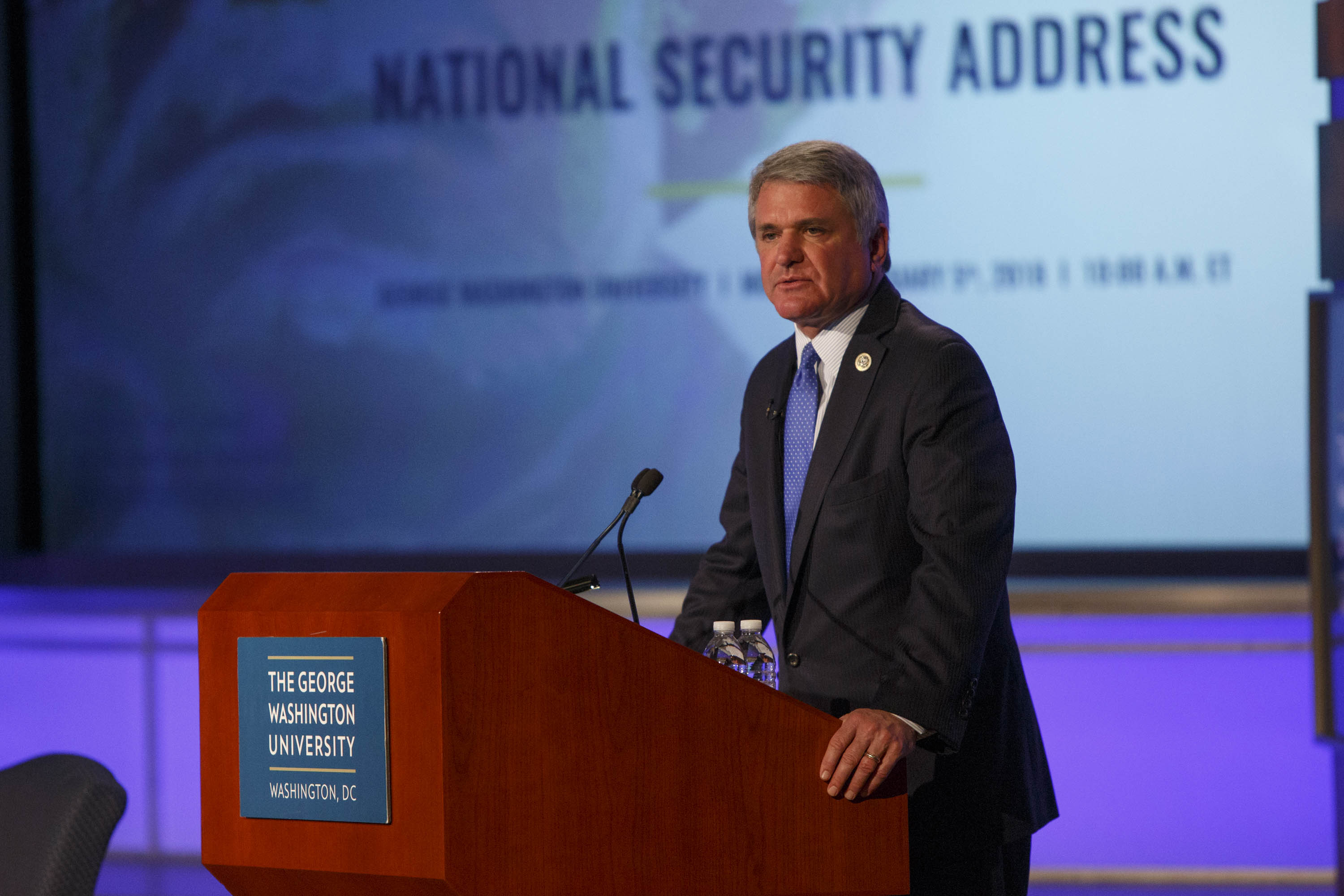
The senator spoke at an event at the George Washington University Science and Technology Exploration Hall in Ashburn, Va., that was co-sponsored by the Northern Virginia Technology Council, an association of businesses, government agencies and service providers in the technology industry. Mr. Warner held a separate meeting with Scott White, the head of the Cybersecurity Degree Completion program, and six undergraduates.
Introducing Mr. Warner, GW President Thomas LeBlanc said as a computer scientist, he is especially proud of the university’s leadership in preparing graduates for the field of cyber security and its investment in research and programs that will make a difference.
Mr. Warner said the U.S. government is still grappling with the Russian disinformation and misinformation campaigns of 2016 even as tactics in the cyber realm are already moving on to “deep fake technology,” where videos and voice recordings are transposed from one person onto another. He said there is nothing in place, no international norms for what is an inappropriate use of cyber technology.
“I would argue that we need both from an American standpoint and with allies and others around the world to try to create ideally a treaty, some level of international cyber norms about activities that are just not acceptable,” he said.
The United States, he maintained, has “extraordinary offensive cyber tools” but has been unwilling to use them out of fear of in-kind responses by adversaries that could escalate.
“I believe that Russia and China believe they are already in a conflict with us. They are already engaged in 21st-century, I hate to use the term ‘war’--but active conflict--with America,” said Mr. Warner, who as vice chair of the Senate Intelligence Committee has argued that the Defense Department spend more on cyber security.
Among the simplest steps a cyber doctrine could take, Mr. Warner said, would be to restrict the number of devices, such as coffee makers and air conditioning systems, now numbering in the millions, that are connected to the internet; liability for products where companies that were notified of a glitch in a system and failed to act, such as the Equifax debacle that resulted in the disclosure of the personal information of hundreds of millions of consumers; and guidelines for social media platforms, such as Facebook, Google and Twitter that may need to be subject to rules similar to other media companies as long as they don’t interfere with innovation.
He said there should also be a debate over the issue of identity validation and compensation for use of personal information.
The biggest obstacle to addressing U.S. cyber vulnerability, he said, is the backlog of security clearances in both the private sector and the government that is now at about 740,000. Since 2014, the time it takes for someone to obtain a security clearance is on average 540 days.
Mr. Warner said some of that could be resolved by taking simple steps such as conducting interviews by Skype rather than in person, penalizing states that do not share criminal records with the federal government and greater reciprocity, allowing a person who has received clearance from a contractor with an agency to move to another without further clearance, which can now take up to 100 days.
“The good news,” Mr. Warner said, is that people in both parties who recognize the country’s cyber vulnerability are pushing back, but “we’ve got a real problem because we have a White House that does not understand the nature of this threat.”