By James Irwin
The Islamic State in Iraq and Syria has proven to be an uncommonly aggressive terrorist organization due to its wealth of resources, infrastructure and public cruelty. A group of experts convened Tuesday at the George Washington University believes the extremist group also is building itself as a cyber security threat.
In remarks delivered at GW’s Virginia Science and Technology Campus that included military, international affairs and media undertones and marked the opening of the university’s Cyber Academy—an initiative that will serve degree-seeking academic programs, provide continuing education training for professionals who tackle cyber threats and facilitate applied research in cyber security—three security experts explained how ISIS has taken old propaganda tactics and combined them with new technology to become a threat in cyberspace.
“This is nothing new. I think somebody in this audience has brought a Snickers bar, and they really weren’t even hungry for chocolate,” said Norman Hayes, a retired rear admiral in the U.S. Navy. “[ISIS] is using tools that are available to everyone. It’s not magic.”
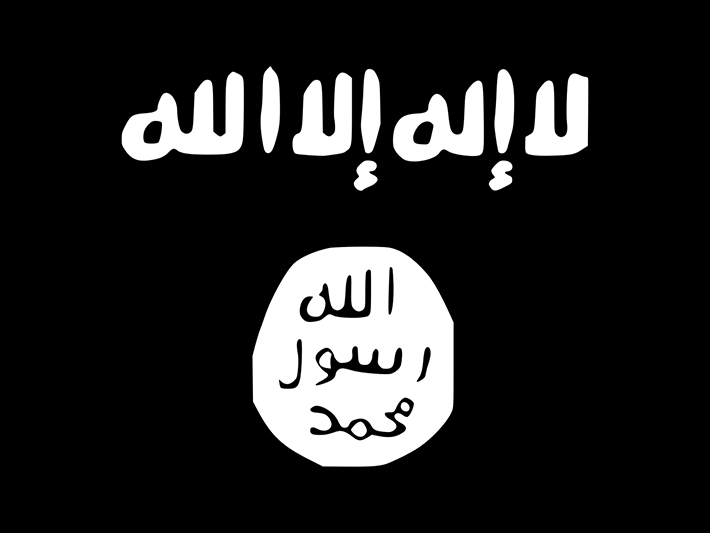
The group, Adm. Hayes said, has used its resources to create an effective media machine for advancing its local and global objectives. As ISIS conquers more territory—often through violence—it sends messages to future towns with a warning to surrender or suffer a similar fate. The group also uses social media to recruit Muslims globally and highlights cruelty instead of downplaying it. “They have a website where they put all their propaganda, and most of it is not in Arabic,” said Gabi Siboni, senior research fellow and the director of two programs at Tel Aviv University’s Institute for National Security Studies.
“Normally, if someone wanted to do bad things, they try to hide it,” said Dr. Siboni, who heads the military and strategic affairs and cyber security programs at TAU. “Here, it is the opposite: [ISIS] wants to be exposed. It wants to show the world.”
 The threat of ISIS recruiting in the cyber world is two-fold, said Norman Hayes, a retired rear admiral in the U.S. Navy. The ISIS propaganda machine has recruited people in the United States, and if some of those people go fight with ISIS without the United States knowing, they can come back home and recruit, undetected. "That's a problem," he said.
The threat of ISIS recruiting in the cyber world is two-fold, said Norman Hayes, a retired rear admiral in the U.S. Navy. The ISIS propaganda machine has recruited people in the United States, and if some of those people go fight with ISIS without the United States knowing, they can come back home and recruit, undetected. "That's a problem," he said.
That tactic, Dr. Siboni said, separates ISIS from other terrorist groups. Al Qaeda, he said, used the Internet extensively, but never went this far in terms of exposing cruelty. The ability for ISIS to communicate and recruit worldwide is a source of power, said Yaacov Ayish, a major general in the Israel Defense Forces and armed forces attaché to the United States and Canada.
“It depends which intelligence organization you are speaking with, but some say you are talking about 20,000 to 50,000 supporters coming into the region from all over the world,” he said. “[ISIS] is highly capable when it comes to psychological warfare—not just terrorizing the tribes and the sects in the region, [but also] terrorizing the international community.”
The group’s capabilities, at least in the cyber world, have been driven by a grasp of both business and media strategy, Dr. Siboni said. ISIS, all three experts agreed, is waging a cyber battle of content and using free media as the apparatus.
“When we talk of the cyberspace threat of ISIS, we’re not talking about ISIS attacking a nuclear facility in the United States tomorrow,” Dr. Siboni said. “This is Western marketing. This is a PR campaign, and they are doing it very successfully. They have a journal, Dabiq, and it’s very well edited. They have it in eight languages.”
 ISIS is attractive because it fills a power vacuum, both physically and in the cyber world, said Yaacov Ayish, a major general in the Israel Defense Forces and armed forces attaché to the United States and Canada. "They are exploiting the fact that there are failed states in Iraq and Syria. They are exploiting the fact that there is no effective military," he said. "And they don’t just receive support from relevant tribes in Iraq and Syria, they recruit all over the world."
ISIS is attractive because it fills a power vacuum, both physically and in the cyber world, said Yaacov Ayish, a major general in the Israel Defense Forces and armed forces attaché to the United States and Canada. "They are exploiting the fact that there are failed states in Iraq and Syria. They are exploiting the fact that there is no effective military," he said. "And they don’t just receive support from relevant tribes in Iraq and Syria, they recruit all over the world."
As for combatting ISIS in cyberspace, Adm. Hayes and Dr. Siboni provided a few ideas—all with hurdles. Cutting ISIS off from the Web would be difficult given the group isn’t bound by geography. Removing content would be costly (though Dr. Siboni believed a Western coalition would eventually have more ability to delete content than ISIS would have to find new avenues to publish). Surveilling Western consumers of ISIS media and intervening before they travel to Syria or Iraq to join the extremist group comes with a host of issues in the wake of Edward Snowden and the National Security Agency leak.
As the U.S.-led coalition against ISIS continues to send more military assets to Iraq and Syria, ISIS’ media power grows, Dr. Siboni said. Articles published by ISIS provide fighters with instructions on how to kill civilians. Dr. Siboni showed a segment of a recently released video of 22 Syrian soldiers being marched to their executions. An analysis of the HD movie by the U.S.-based Terrorism Research and Analysis Consortium and the UK-based counter-extremism group Quilliam revealed it took at least six hours to create, involved several takes and cost at least $200,000 to produce.
“It’s not like the execution was filmed. They picked the soldiers for the sake of making the movie,” he said. “There was a movie to make, and they used real life to create it. They are doing this to create terror, fear and chaos and also to recruit.”