By Tatyana Hopkins
Most people think hackers need advanced technical skills or have to contact their targets through fraudulent calls or emails to obtain personal and confidential information, but a growing number of them are actually getting sensitive information through companies’ over-the-phone customer service, said Rachel Tobac, CEO of SocialProof Security.
She said call center fraud continues to grow since its unprecedented 113 percent jump between 2015 and 2016 and cited outdated phone authentication protocols as the reason.
“We are living in the dark ages on the phone compared to how hard it is to break into accounts online,” Ms. Tobac said. “Can you imagine if you were trying to log into your Gmail and all you needed to log into the website was your birthday and your address? No. Of course, you would use your password and a two-factor code. But that’s how it is over the phone right now.”
Ms. Tobac helps people and companies keep their data safe by testing their protected systems and networks to expose vulnerabilities before malicious hackers exploit them using social engineering—a form of hacking that uses persuasion to manipulate people into disclosing compromising information.
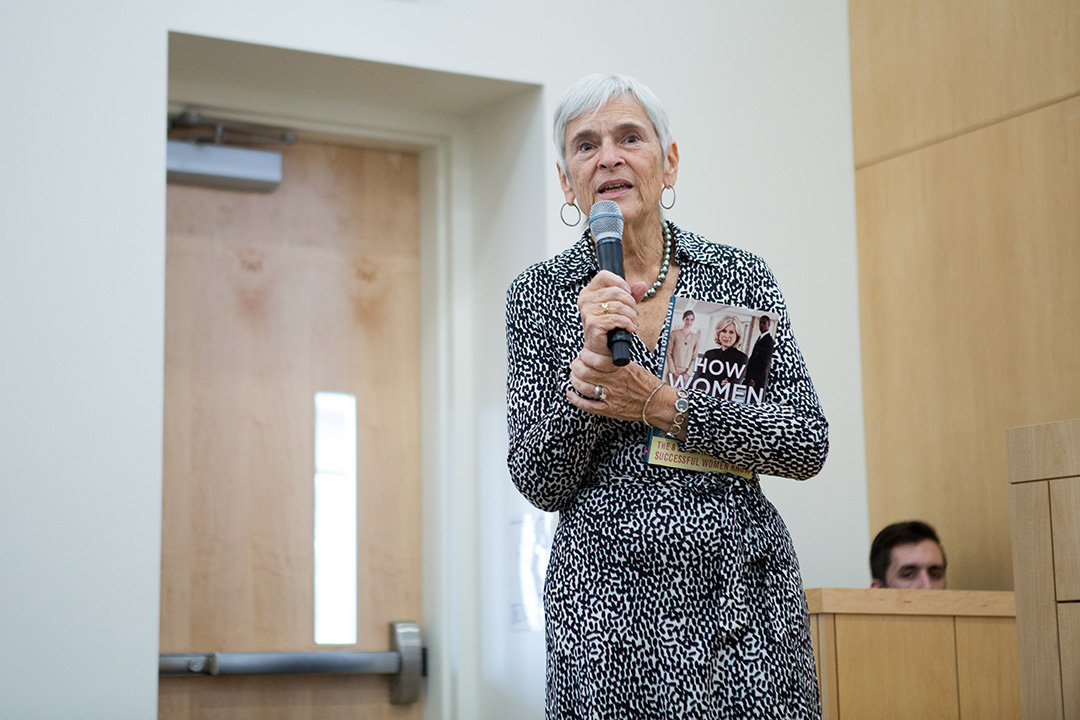
She spoke Wednesday in the Jack Morton Auditorium about how hackers gain personal information through call centers and how it can be prevented as part of a National Cyber Security Awareness Month event hosted by George Washington University Information Technology.
She was joined by CNN technology reporter Donie O’Sullivan, whose accounts she hacked live at this year’s DEF CON, one of the world’s largest hacker conventions. She is a three-time winner of the convention’s Capture the Flag competition, where hackers attack a company in front of crowds and entirely over the phone.
Mr. O’Sullivan asked Ms. Tobac to take over as many of his accounts as she could. By the end of the day, she hacked more than 10 of his accounts, siphoned thousands of dollars-worth of points into accounts she controlled, changed his travel plans and was even prepared to cut his electricity off and lock him out of his phone.
She said while Mr. O’Sullivan expected her to contact him for information, she hacked him through his service providers instead.
“All I needed to be able to access his accounts, and in some cases lock him out completely, was his full name, his current address, whole birthday, all of his email addresses and all of his phone numbers,” she said.
Ms. Tobac and Mr. O’Sullivan gave live re-enactments of the calls.
[video:https://youtu.be/LYilP-1TwMg width:100% align:center lightbox_title:Rachel Tobac ]
Learning what she could about Mr. O’Sullivan through publicly available information online and his social media accounts, she called companies he had posted about using a voice changer and software to make it seem as if she were calling from his number.
To get his address, she called a furniture company and claimed to be his wife, saying she wanted to check that the company had his correct address on file before she placed another order. She deliberately gave the wrong address so that the person on the other end of the line would correct her with his full home address.
She used a similar method to obtain his phone number from a hotel he tagged on Instagram.
“We need to update our authentication protocols over the phone so that people like me don't try to leverage the other people over the phone to do things that they shouldn't be able to do,” Ms. Tobac said.
She said companies should start using the types of multistep verification methods on the phone that are used online including initiating call backs to the number on file or sending codes to the email or phone on file.
“It’s pretty straight forward,” Ms. Tobac said. While customers wait for updated phone verification protocols, she said they should avoid naming products, companies and services they used on social media and use services like DeleteMe by Abine to remove their information from online data broker websites.
She also said people should demand that their service providers update their security protocols.
“It is not your fault if you get [your personal information hacked] because a company gives away your data,” Ms. Tobac said. “The point is action. I want you to understand how you can keep yourself safe and what to demand of your companies so they can update their protocols.”